 One of Checkpoint’s customer’s employee downloaded a malicious app called “EnergyRescue” which consisted of zero day mobile ransomeware (Doxware)from Google Play store. The ransomeware dubbed “Charger” and has appeared to be downloaded by millions of Android users.
One of Checkpoint’s customer’s employee downloaded a malicious app called “EnergyRescue” which consisted of zero day mobile ransomeware (Doxware)from Google Play store. The ransomeware dubbed “Charger” and has appeared to be downloaded by millions of Android users.
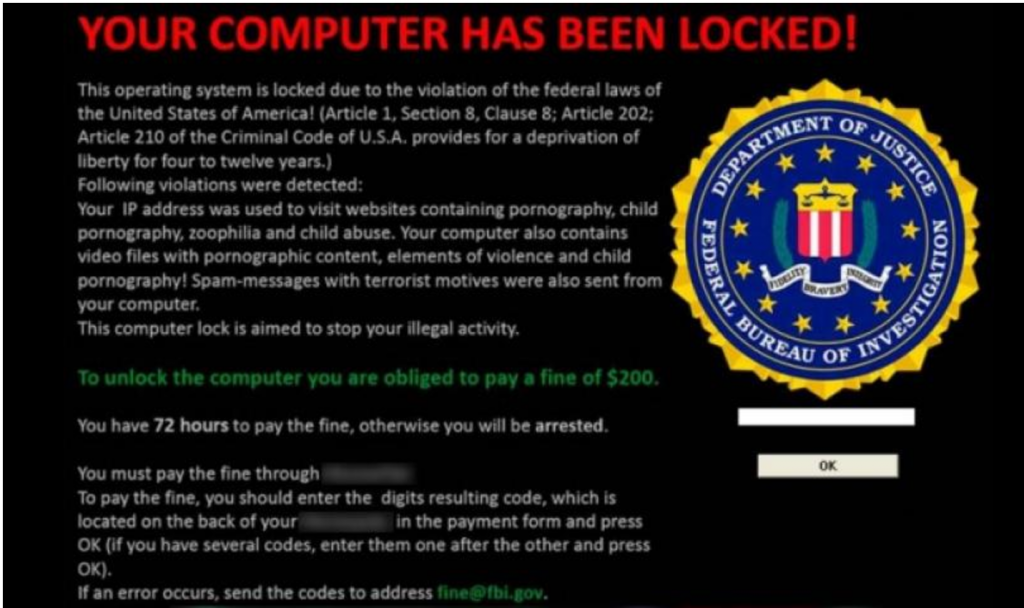
The ransomeware infected app gets access to contacts and SMS messages from the user’s device requesting admin permissions appears to be genuine. Once the admin permission is granted, the ransomware locks the device and requests the ransom from the victim for .2 bitcoins which is almost 180$. This amount is pretty high for the same category which has been seen lately.
The ransomware demands the money or else threatens to post the user data online every 30 minutes.
“You need to pay for us, otherwise we will sell portion of your personal information on black market every 30 minutes,WE GIVE 100% GUARANTEE THAT ALL FILES WILL RESTORE AFTER WE RECEIVE PAYMENT. WE WILL UNLOCK THE MOBILE DEVICE AND DELETE ALL YOUR DATA FROM OUR SERVER!TURNING OFF YOUR PHONE IS MEANINGLESS, ALL YOUR DATA IS ALREADY STORED ON OUR SERVERS! WE STILL CAN SELLING IT FOR SPAM, FAKE, BANK CRIME etc… We collect and download all of your personal data. All information about your social networks, Bank accounts, Credit Cards. We collect all data about your friends and family.“
The malware contains a dropper which attracts real malicious components to the mobile device.
Hence the real impact is unknown but this app has infected millions of users worldwide. Recommendation can be found here
