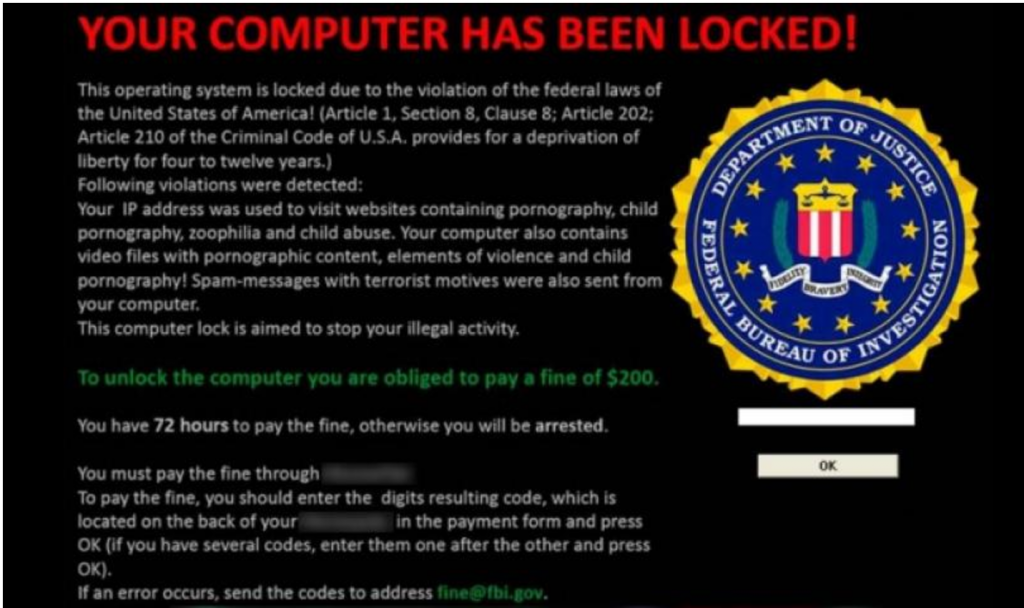
 As security controls and defense measures for computer systems become more sophisticated, cyber criminals have taken one step ahead in the world of Ransomware. The most profitable ransomware attacks has taken a leap with doxing.
As security controls and defense measures for computer systems become more sophisticated, cyber criminals have taken one step ahead in the world of Ransomware. The most profitable ransomware attacks has taken a leap with doxing.
What is Doxware ?
“Ransomware is the art of encrypting data on a network, users PC or Mac and asking for a ransom amount to decrypt it. With Doxware the criminals encrypt the data locally on the network and also copy the same to their own server and ask for ransom. If ransom is not paid then the sensitive information is posted publicly.”
The threat has increased two fold with Doxware with the risk of sensitive information going public if ransom is not paid.
Earlier if companies or individuals who regularly backed up their systems could easily wipe off and rebuild their machines if infected by ransomware. But now users who are a victim of the ransomware attacks are forced to pay the ransom to protect the reputation and sensitive information.
Malwarebytes was one of the first companies to report on this issue and they have identified at least 5 different variants of Doxware in the recent months since mid of last year. Doxware is not widespread as much as ransomware for now but this is predicted to increase during 2017 for targeted.
It’s very effective and a easy money for criminals by holding the victim hostage with their data. Currently only windows versions have been discovered as per Malwarebytes and it won’t be long before other operating systems are caught up. Universities, Government agencies, hospitals and many such sectors may end up paying instead of fighting against it as it’s a matter of sensitive data of going public verses money.
Prevention:
There is no fool proof prevention at this point but companies like Malwarebytes and Kaspersky have known definitions to stop some of the variants. Ultimately the end user must be cautious when clicking links while on the internet, have AV installed , have the latest patches for their Operating systems and possibly use a reputation based url checker integrated with their browsers.
