Trend micro researchers have discovered a Android Trojan ad library named Xavier that steals user’s information without user knowledge. More than 800 Android apps which embedded the ad library appears to have infected with the malware. Xavier has self-protect mechanism that allows it to escape both static and dynamic analysis making it harder to detect. It can also download additional pieces of codes or scripts which can be very dangerous based on the intention of malware actions.
These identified Android apps have been downloaded by millions of people around the world which puts the entire Android ecosystem to risk.
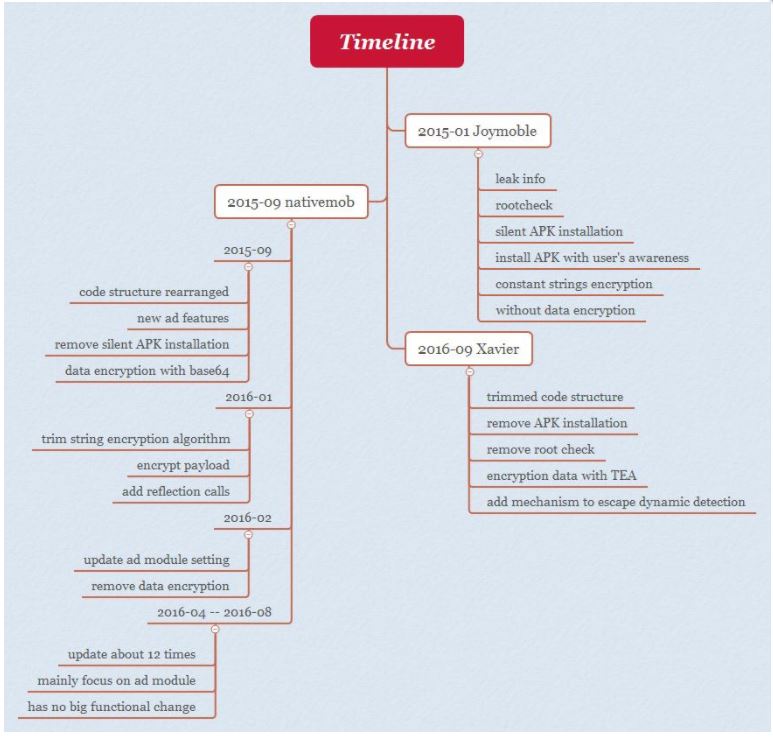
Xavier Trojan is a member of the AdDown family, which has existed since 2015. The first version was called as joymobile which had the capability of remote code execution.
The current version can evade detection and adds information stealing module in addition to previous remote code execution. The infected apps appears to be found primarily in South Asian countries such as Vietnam, Philippines, Indonesia, Thailand, Taiwan and few others.
Pic from TrendMicro
Technical details of this malware can be found at Trend blog here
Indicators of Compramise : https://documents.trendmicro.com/assets/appendix-analyzing-xavier-an-information-stealing-ad-library-on-android.pdf