Researchers from Symantec have identified a PC Trojan which can compromise Android smartphone by installing ‘malware ‘when connected via PC.
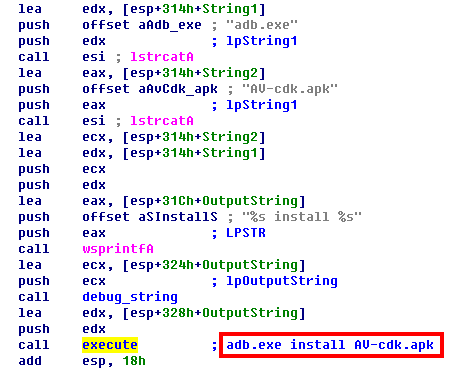
The Windows Variant is known as Trojan.Droidpak, drops a malicious DLL to the windows system and registering DLL as a windows service. Then the DLL downloads a configuration file (from active remote server) that downloads a malicious APK file for future installation on any detected Android devices.
Additionally the DLL also installs a Android Debug Bridge software, used it to install the malicious APK file onto any detected victim( Android devices) that are connected to the computer. Once the malware is installed via windows system, the malware attempts to hide its presence by posing as a “Google App Store” application. The malicious APK is a variant of Android.Fakebank.B which poses as a Google APP Store application.Once the malicious app is installed it secretly searches for online banking apps that the user has installed in the background.
The USB debugging Mode has to be enabled on the Android device for this attack to take place. Additionally the malicious app intercepts texts on the infected Android phone.
Symantec recommends the following to remain safe as preventive measure
- Turning off USB debugging on Android device when not using it
- Caution when connecting Android mobile device to unknown/untrustworthy computers
Symantec further states that “We’ve seen Android malware that attempts to infect Windows systems before. Android.Claco, for instance, downloads a malicious PE file along with an autorun.inf file and places them in the root directory of the SD card. When the compromised mobile device is connected to a computer in USB mode, and if the AutoRun feature is enabled on the computer, Windows will automatically execute the malicious PE file.”