French security engineer Eloi Vanderbeken discovered a backdoor that can reset linksys and netgear settings to factor settings and therefore the username and password.
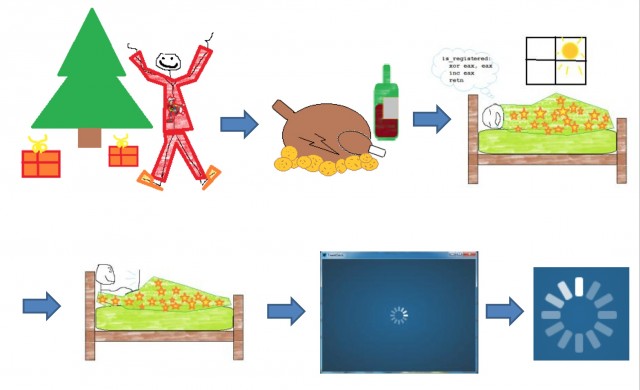
Vanderbeken discovered this backdoor on his own Linksys WAG200G wireless DSL router, after deciding to limit the bandwidth used by his holiday guests and remembering he forgot the complex username and password combination he chose for accessing the router’s administration panel as reported on net-security.org
He experimented on his router and discovered that a a unknown service was listening on TCP port 32764 was evident. SANS also published this other day on this issue as well. The service accepts 13 types of messages, in which two allowed him to get into configuration settings and the other that restored the router to its default factory settings.
“After sharing the colourful details of his “quest” on his Github account, other hackers around the world took it upon themselves to check what other routers have the same backdoor. Unfortunately, there are quite a few. The list allowed people to speculate that the affected devices have one thing in common: they have been manufactured by Sercomm, a firm that builds routers both under its own name and for several other companies, including Linksys and Netgear.” – net-security.org reports