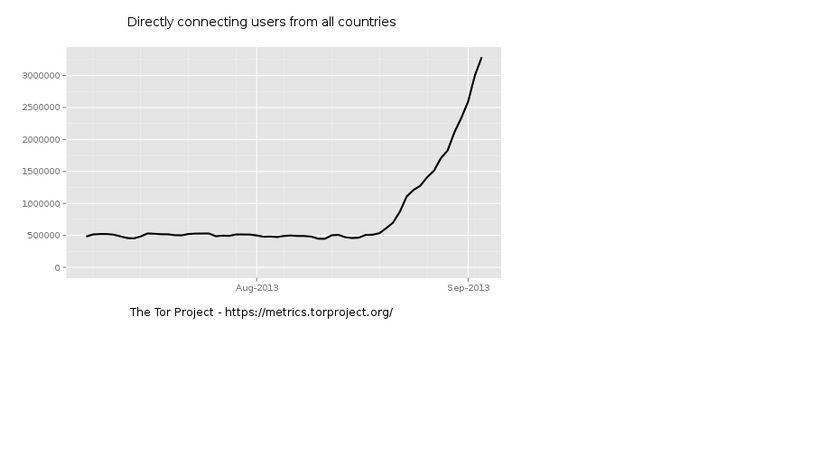
Recently Roger from posted a question regarding increased traffic on TOR network. After NSA’s surveillance the first suspect was assuming internet users have started using tor network to surf anonymously. However the exponential increased intraffic showed its something more than just the users. The suspect was it must be a botnet.
Even Arma posted saying “Starting around August 20, we started to see a sudden spike in the number of Tor clients. By now it’s unmistakable: there are millions of new Tor clients and the numbers continue to rise”
“The fact is, with a growth curve like this one, there’s basically no way that there’s a new human behind each of these new Tor clients. These Tor clients got bundled into some new software which got installed onto millions of computers pretty much overnight. Since no large software or operating system vendors have come forward to tell us they just bundled Tor with all their users, that leaves me with one conclusion: somebody out there infected millions of computers and as part of their plan they installed Tor clients on them,” as described by Tor officials described on their blog.
“It doesn’t look like the new clients are using the Tor network to send traffic to external destinations (like websites). Early indications are that they’re accessing hidden services — fast relays see “Received an ESTABLISH_RENDEZVOUS request” many times a second in their info-level logs, but fast exit relays don’t report a significant growth in exit traffic. One plausible explanation (assuming it is indeed a botnet) is that it’s running its Command and Control (C&C) point as a hidden service.”
After analyzing this Fox-IT blog wrote “Previously, the botnet communicated mainly using HTTP as well as alternative communication methods. More recently and coinciding with the uptick in Tor users, the botnet switched to Tor as its method of communication for its command and control channel. The botnet appears to be massive in size as well as very widespread. Even prior to the switch to Tor, it consisted of tens of thousands of confirmed infections within a limited amount of networks. When these numbers are extrapolated on a per country and global scale, these are definitely in the same ballpark as the Tor user increase,”