Petya has impacted all over the world starting from pharmaceutical companies, oil gaints, airports, hospitals, ports and many banks. The method of infection is similar to Wannacry with leaked NSA EthernalBlue, (MS17-010) infected thousands of people including hospital networks.
Petya differs from typical ransomware as it also overwrites and encrypts the master boot record (MBR) along with encrypting files. This has been around since 2016. The security researchers also found a version of Petya which is nonPetya. The “NotPetya” attack had hit 2,000 users in Russia, Ukraine, Poland, France, Italy, the UK, Germany and the US, Kaspersky said.
NotPetya is lot different as it finds passwords on the infected system to move to other systems either extracting passwords from memory or from the local file system. It can also abuse psexec tool making it to execute malicious code on other computers . In other words, if the administrator system is infected, it has the potential to infect the entire network.
The infected computer may perform the following actions:
- Propagation may be using RDP or SMB protocols
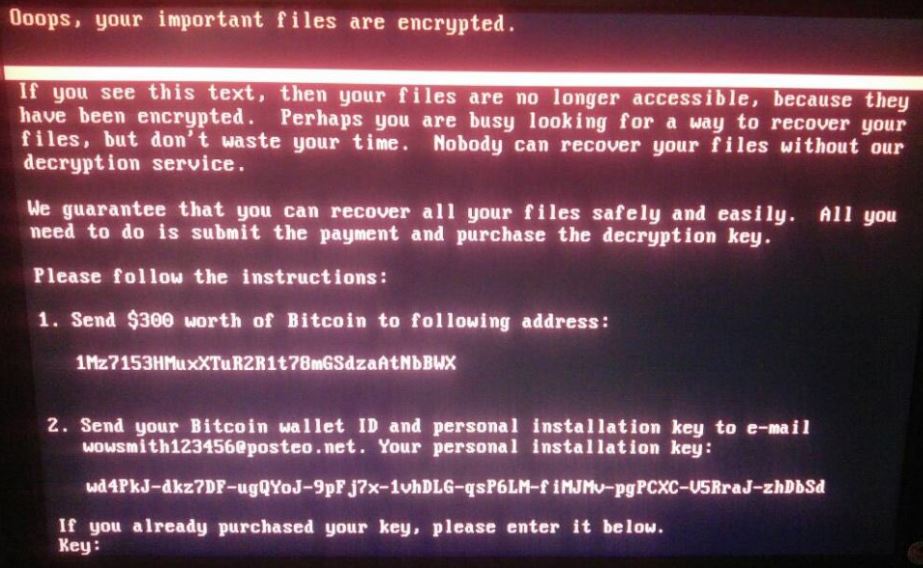
- The ransomware will display the above message
- Once infection is done a reboot may prompt the above screen.
Ukraine’s Ukrenego electricity supplier, Ukraine’s central bank, state telecom, municipal metro, and Kiev’s Boryspil Airport were reported to have been infected.Later in the day Danish shipping company Maersk,Russian logistics arm Damco, Russian oil company Rosneft reported to have been impacted. There have also been several recorded cases in the United States, including the pharmaceutical company Merck, a Pittsburgh-area hospital.
The full impact of this ransomware is yet to be known and we hope it limits its impact in this information age.