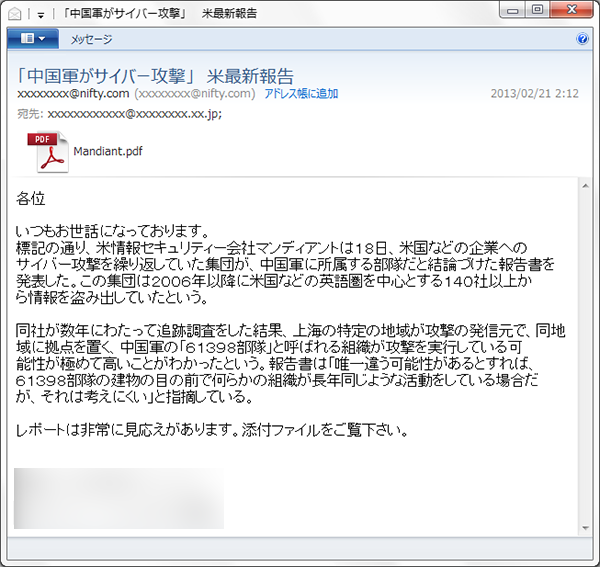
Symantec and few others reported about the multiple versions of APT – 1 infecting thousands of computers worldwide. The hackers are using multiple versions of Apt 1 tricking the users download the pdf.
As per Mandiant blog report.
As we noted yesterday, Brandon Dixon’s 9B+ blog and Symantec reported the discovery of two malicious versions of our APT1 report. We wanted to provide follow-on details based on our analysis of these samples. Additionally, we have attached Indicators of Compromise (IOCs) so folks can begin using them to detect the malware.
PDF1 – “Mandiant_APT2_Report” Lure
MD5: 14A6E24977FF6E7E8A8661AADFA1A1F3
This is a password protected PDF using the password “hello” and exploits the CVE-2011-2462 vulnerability from back in December of 2011. Once opened it drops
%TEMP%\AdobeArm.tmp(4D9A1144E08E7FAE7D6DB8BC606F5BE5) and%TEMP%\Mandiant_APT2_Report.pdf(29E9494E2EBA1D8F8AD9EE308FFE53EF). The newly dropped report is opened and theAdobeArm.tmpbinary is executed.– See more at: https://www.mandiant.com/blog/threat-actors-mandiant-apt1-report-spear-phishing-lure-nitty-gritty/#sthash.Ds1gumcA.dpuf
Screenshot from Symantec